Penetration Testing
Penetration Testing (Pentesting) is a simulated cyberattack on a computer system, network, or web application to identify vulnerabilities that could be exploited by attackers. It’s like a fire drill for cybersecurity, helping organizations understand and improve their defenses.
General Pentesting scope:
Network Penetration Testing: Targets network infrastructure like servers, firewalls, and switches.
Web Application Penetration Testing: Focuses on vulnerabilities in web-based applications.
Wireless Penetration Testing: Identifies risks in wireless networks.
Physical Penetration Testing: Assesses physical security measures.
Social Engineering Penetration Testing: Exploits human psychology to gain access to systems.
Client-Side Penetration Testing: Targets vulnerabilities in client-side applications.
IoT Penetration Testing: Evaluates security in Internet of Things devices.
Mobile App Penetration Testing: Assesses security in mobile applications.
Red Team Penetration Testing: Simulates a full-scale attack to test defenses
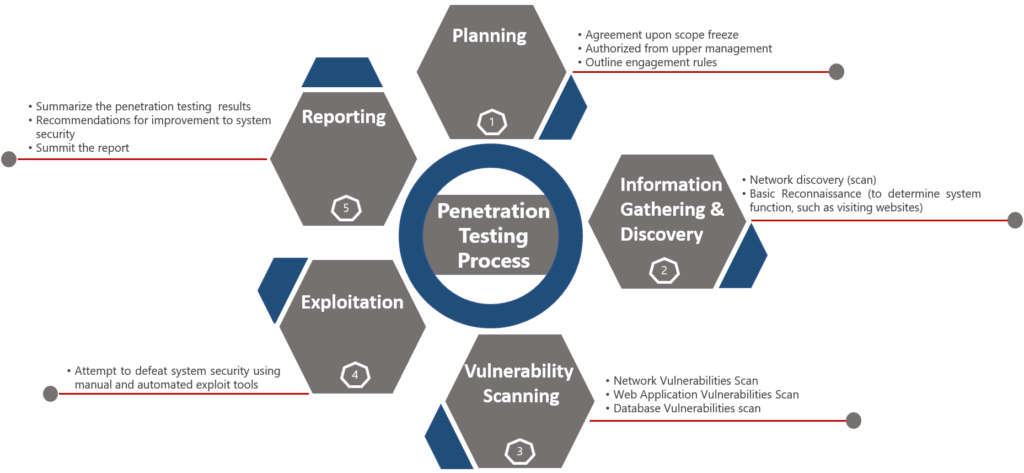
1. Planning
This phase is very crucial in initiating any engagement for pen testing.
Below are the main activities covered as part of planning:
Agreement upon the scope of the project.
Authorize the overall engagement plan from the upper management.
Outline engagement rules.
2. Information Gathering & Discovery
Below are the main activities covered as part of Information gathering and discovery phase:
Run the Network discovery scan.
Perform basic Reconnaissance to gather intelligence (e.g., network information, domain names)
3. Vulnerability Scanning
Below are the main activities carried out as part of the Vulnerability Scanning phase:
As per the agreed scope perform various scans. Utilize tools to identify potential entry points.
Network Vulnerabilities Scan
Web Application Vulnerabilities Scan
Database Vulnerabilities scan
Understand how the target application responds to intrusion attempts.
4. Exploitation
Below are the main activities performed in this phase:
Attempt to defeat system security using manual and automated exploit tools
Exploit vulnerabilities to gain access to the target.
Establish control over the target system.
5. Reporting
Below are the main activities performed in this phase. This phase is more on documenting the findings and closing the engagement.
Summarize the penetration testing results
Recommendations for improvement to system security
Summit the report
*Once Report is submitted, it depends on the agreement between the organization and the vendor to engage in fixing the vulnerabilities also or some organization internal teams would fix the identified vulnerabilities to secure the environment.
Mode of Pentesting
There is various ‘mode’ of engagements when it comes to perform a Pen test.
- 1. Blind Pentesting: In Blind Penetration Testing, the testers have no prior knowledge of the target system. They perform the test as if they were real attackers, uncovering vulnerabilities that might be missed by the organization.
- 2. Double Blind Pentesting: In Double Blind Penetration Testing, neither the penetration testers nor the target organization’s IT/security team are aware of the test. This simulates a real-world attack scenario, providing a realistic assessment of the organization’s readiness and response procedures.
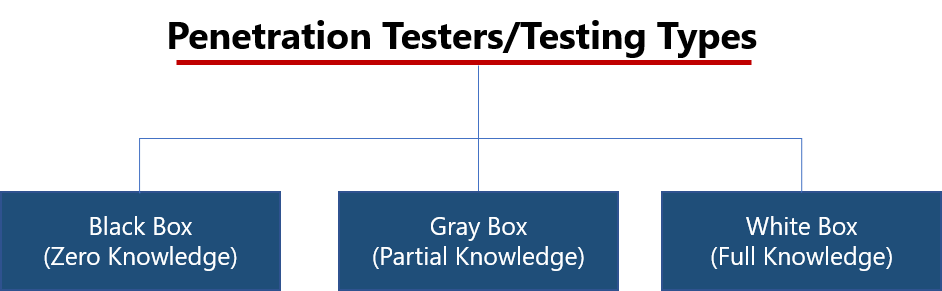
Penetration Testers/Testing Types
Let’s delve into the different types of penetration testing: Black Box (Zero Knowledge), Gray Box (Partial Knowledge), and White Box (Full Knowledge).
- 1. Black Box (Zero Knowledge): In Black Box Testing, the tester has no prior knowledge about the target system, application, or network. The tester approaches the test as an outsider or an external hacker would.
Advantages: Provides a realistic scenario of an external attack and helps identify external-facing vulnerabilities.
Disadvantages: May be time-consuming and might not uncover all vulnerabilities due to the lack of internal knowledge.
- 2. Gray Box (Partial Knowledge): In Gray Box Testing, the tester has limited knowledge of the target system, application, or network. This knowledge could include login credentials, network architecture diagrams, or partial source code.
Advantages: Balances the realism of an external attack with the efficiency of having some insider knowledge, leading to potentially more comprehensive results.
Disadvantages: May still miss some vulnerabilities that a more thorough (White Box) examination would reveal.
- 3. White Box (Full Knowledge): In White Box Testing, the tester has full knowledge of the target system, application, or network, including access to source code, architecture diagrams, and configuration files.
Advantages: Provides a thorough and comprehensive assessment, identifying vulnerabilities that other types of tests might miss.
Disadvantages: Less realistic in simulating an actual external attack and might require more time and resources.
InfoKavach Academy is proudly powered by WordPress